Sending Domain Setup
A sending domain authenticates your outgoing emails with DKIM and DMARC, ensuring they are delivered reliably and not marked as spam. This requires a CNAME record for domain verification, a TXT record for DKIM signing, and a TXT record for DMARC policy. To create a sending domain in Lettr:- Select Domains in the navigation panel
- Select Sending Domains
- Click Create Sending Domain
- Enter your desired sending subdomain (e.g.
mailing.company.com) - Click Create Domain
Configure Azure DNS
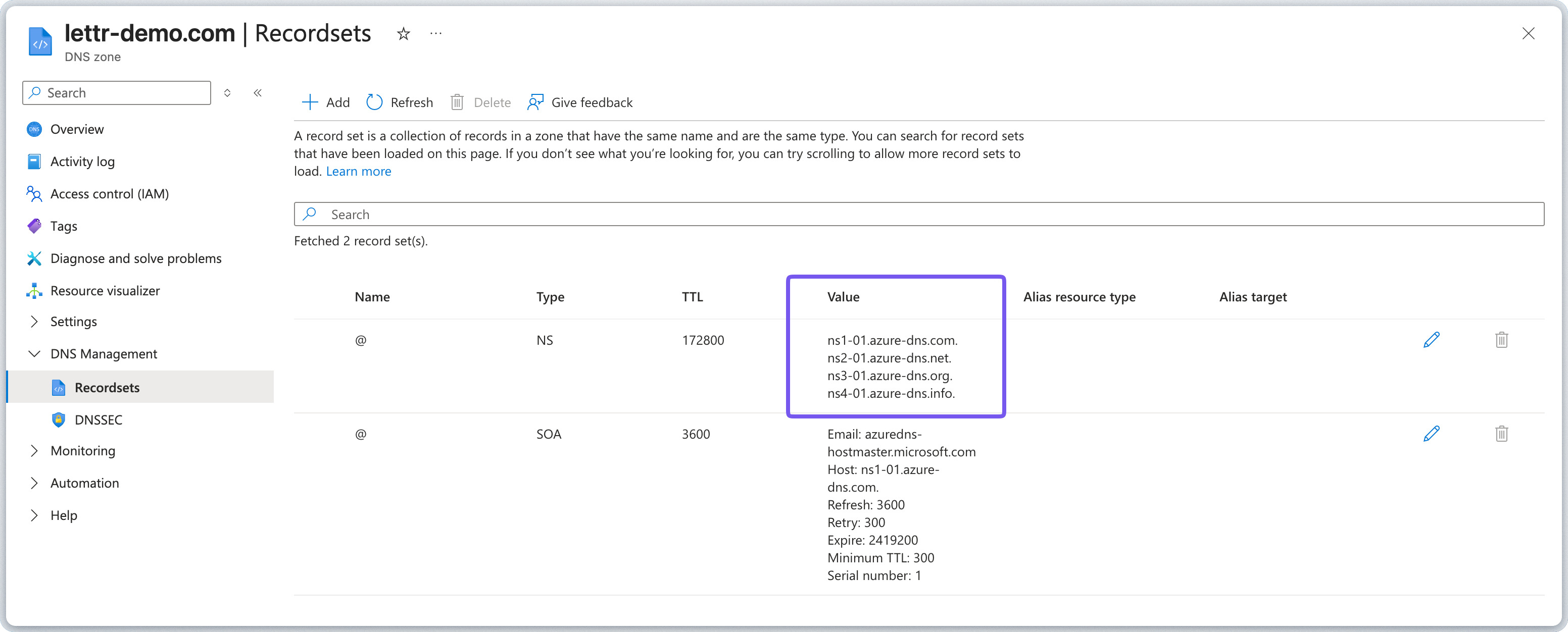
Log in to the Azure Portal and navigate to All services in the left-hand menu. Search for DNS zones to view your zones, and select the zone that matches your domain.Domain registered with a different registrar?
Domain registered with a different registrar?
If you registered your domain elsewhere but want to manage DNS on Azure, you must first create a DNS zone in Azure DNS
and then update the nameservers at your registrar to Azure’s nameservers shown in the zone overview.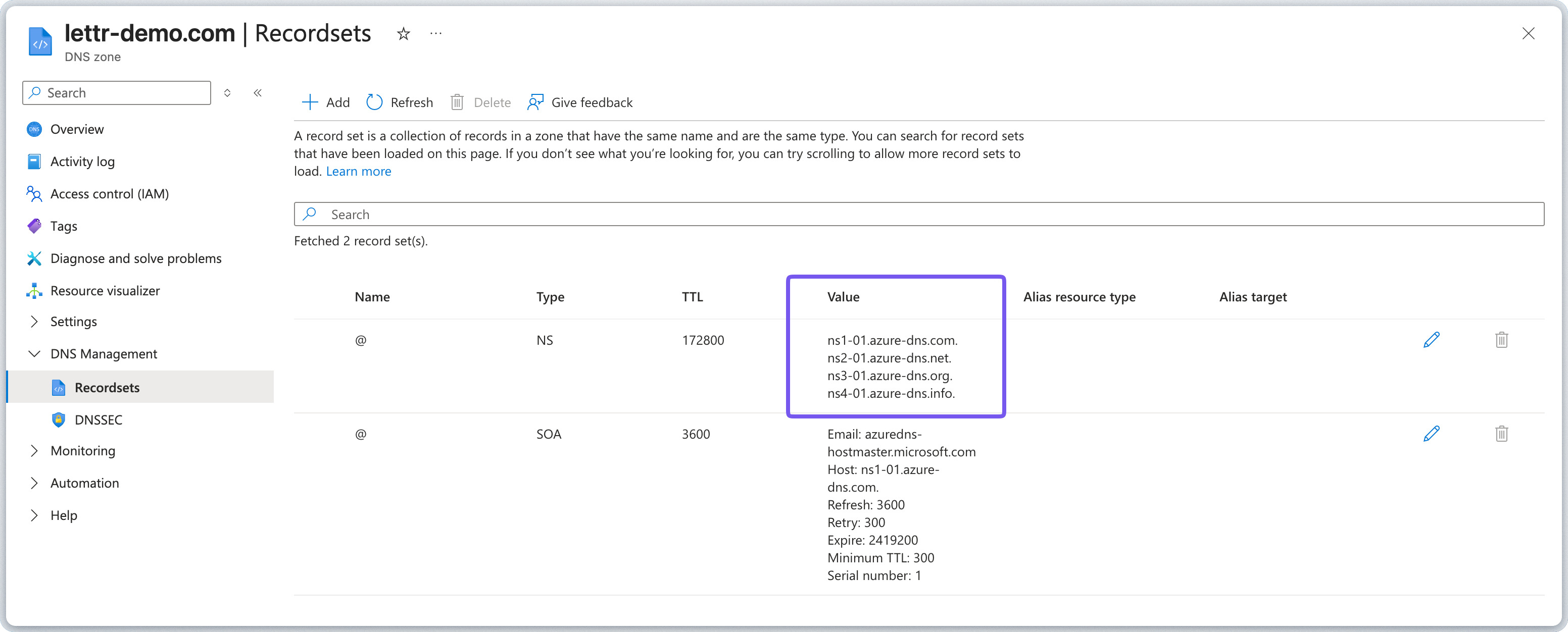
Add CNAME Record
The CNAME record verifies domain ownership with Lettr’s email infrastructure. Add the record in Azure DNS:- Click + Add in your DNS zone.
- Enter the Hostname from Lettr (without your domain suffix) into the Name field. For example, paste only
mailing, notmailing.company.com. - Set Type to CNAME.
- Leave TTL and TTL unit at their defaults (1 Hour).
- Enter the Value from Lettr into the Alias field.
- Click Add.
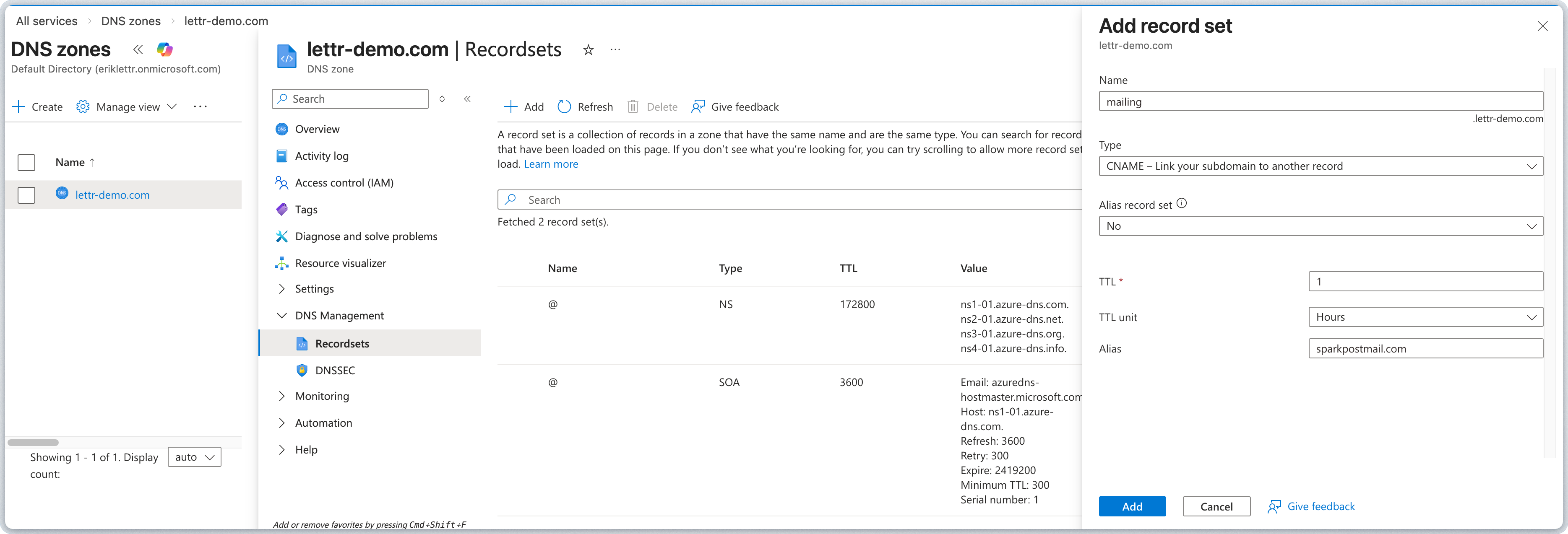
Azure DNS automatically appends your zone name to the record name. Always paste only the subdomain portion (e.g.
mailing, not mailing.company.com).Add TXT Record (DKIM)
The DKIM record adds a cryptographic signature to your outgoing emails, allowing recipients to verify they were sent by an authorized sender. Add the record in Azure DNS:- Click + Add in your DNS zone.
- Enter the Hostname from Lettr (without your domain suffix) into the Name field. For example, paste only
scph0126._domainkey.mailing. - Set Type to TXT.
- Leave TTL and TTL unit at their defaults (1 Hour).
- Enter the Value from Lettr into the Value field.
- Click Add.
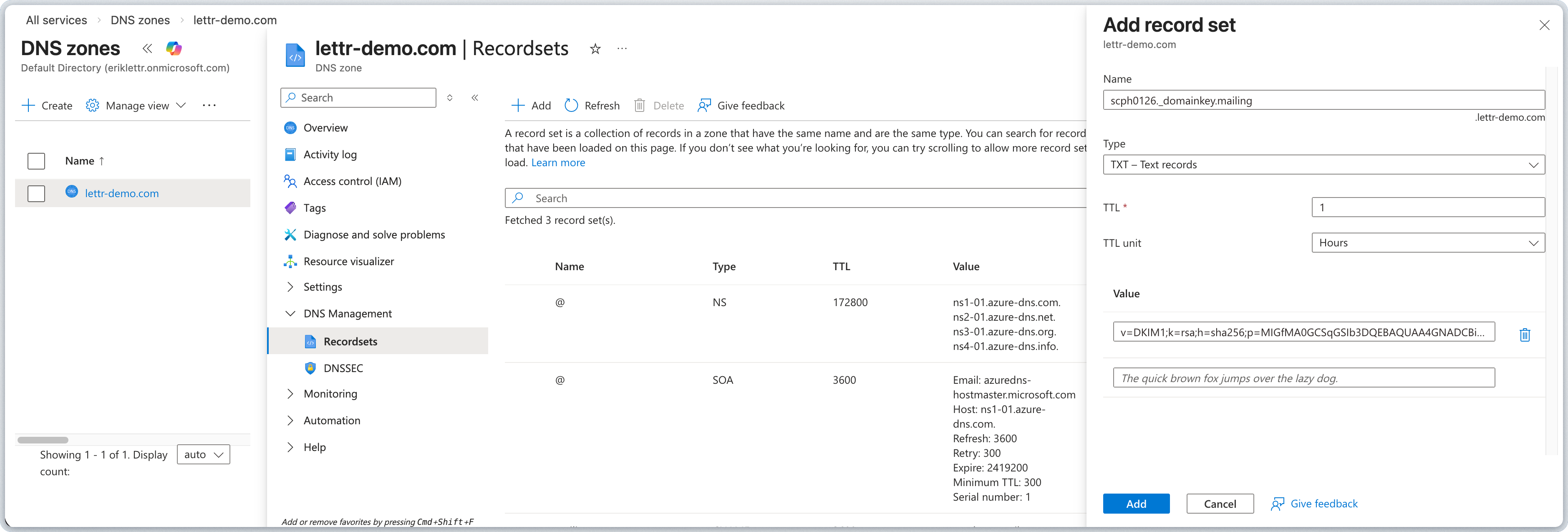
Azure DNS automatically appends your zone name to the record name. Always paste only the subdomain portion (e.g.
scph0126._domainkey.mailing, not scph0126._domainkey.mailing.company.com).DKIM values are long strings. After saving, re-open the record set to confirm the full value was stored correctly. If
it appears truncated, delete and re-add the record.
Add TXT Record (DMARC)
The DMARC record tells receiving mail servers how to handle emails that fail authentication checks, protecting your domain from spoofing. Add the record in Azure DNS:- Click + Add in your DNS zone.
- Enter the Hostname from Lettr (without your domain suffix) into the Name field. For example, paste only
_dmarc.mailing. - Set Type to TXT.
- Leave TTL and TTL unit at their defaults (1 Hour).
- Enter the Value from Lettr into the Value field.
- Click Add.
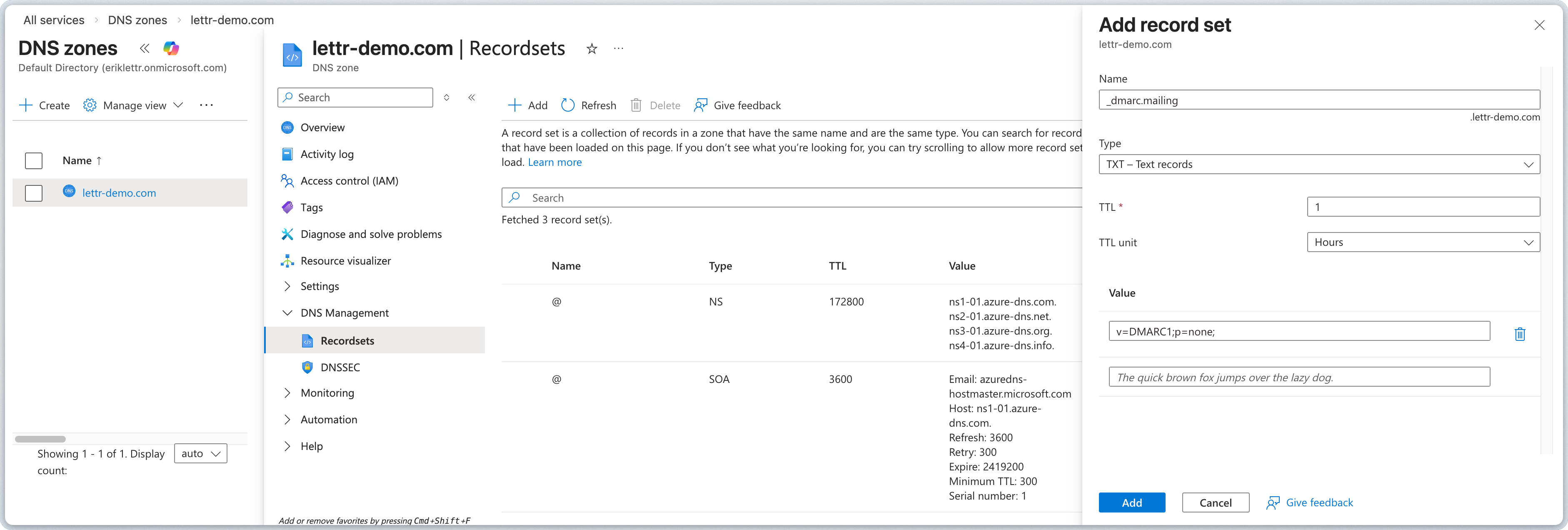
Azure DNS automatically appends your zone name to the record name. Always paste only the subdomain portion (e.g.
_dmarc.mailing, not _dmarc.mailing.company.com).Verify Your Sending Domain
After adding all three DNS records, go back to Lettr and click Verify DNS Records. DNS propagation can take up to 24–48 hours, though it typically completes within a few minutes.Inbound Domain Setup
An inbound domain allows Lettr to receive emails on your behalf. This requires three MX records that direct incoming mail to Lettr’s mail servers.Add Inbound Domain to Lettr
To create an Inbound domain in Lettr:- Select Domains in the navigation panel
- Select Inbound Domains
- Click Create Inbound Domain
- Enter your desired inbound subdomain (e.g.
inbound.company.com) - Click Create Domain.
Add MX Records
MX records tell other mail servers where to deliver emails addressed to your domain. Add the MX record set in Azure DNS:- Click + Add in your DNS zone.
- Enter the Hostname from Lettr (without your domain suffix) into the Name field. For example, paste only
inbound. - Set Type to MX.
- Leave TTL and TTL unit at their defaults (1 Hour).
- Under MX Records, enter
10for Preference andrx1.sparkpostmail.comfor Mail exchange. - Add two more rows:
10/rx2.sparkpostmail.comand10/rx3.sparkpostmail.com. - Click Add.
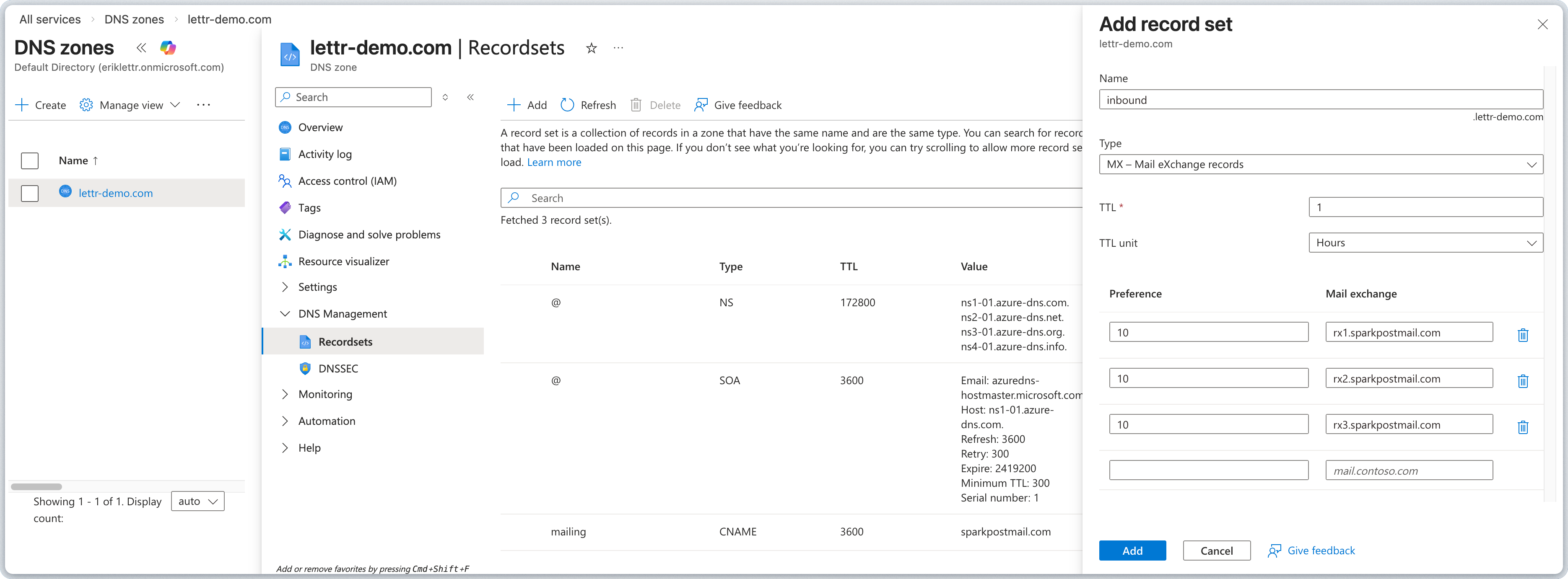
Azure DNS automatically appends your zone name to the record name. Always paste only the subdomain portion (e.g.
inbound, not inbound.company.com).Verify Your Inbound Domain
After adding all three MX records, go back to Lettr and click Verify DNS Records. DNS propagation can take up to 24–48 hours, though it typically completes within a few minutes.Tracking Domain Setup
A tracking domain allows Lettr to track email opens and link clicks using your own custom domain instead of the default Lettr tracking domain. This requires two CNAME records: one for the SSL certificate and one for routing tracking traffic to Lettr’s infrastructure.Add Tracking Domain to Lettr
To create a Tracking domain in Lettr:- Select Domains in the navigation panel
- Select Tracking Domains
- Click Create Tracking Domain
- Enter your desired tracking subdomain (e.g.
tracking.company.com) - Click Create Domain
Add SSL Certificate CNAME Record
The SSL Certificate CNAME record provisions an SSL certificate for your custom tracking domain, enabling secure HTTPS connections for tracked links. Add the record in Azure DNS:- Click + Add in your DNS zone.
- Enter the Hostname from Lettr (without your domain suffix) into the Name field.
- Set Type to CNAME.
- Leave TTL and TTL unit at their defaults (1 Hour).
- Enter the Value from Lettr into the Alias field.
- Click Add.
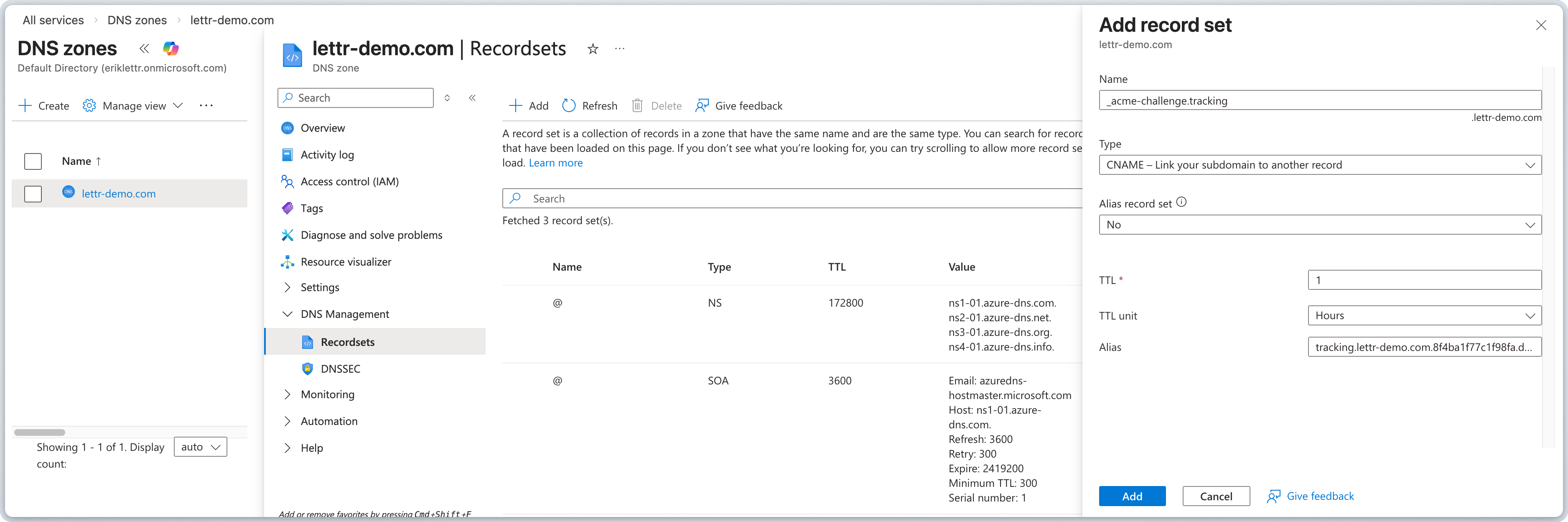
Azure DNS automatically appends your zone name to the record name. Always paste only the subdomain portion (e.g.
tracking, not tracking.company.com).Add Traffic CNAME Record
The Traffic CNAME record routes click and open tracking requests from your custom domain to Lettr’s tracking servers. Add the record in Azure DNS:- Click + Add in your DNS zone.
- Enter the Hostname from Lettr (without your domain suffix) into the Name field.
- Set Type to CNAME.
- Leave TTL and TTL unit at their defaults (1 Hour).
- Enter the Value from Lettr into the Alias field.
- Click Add.
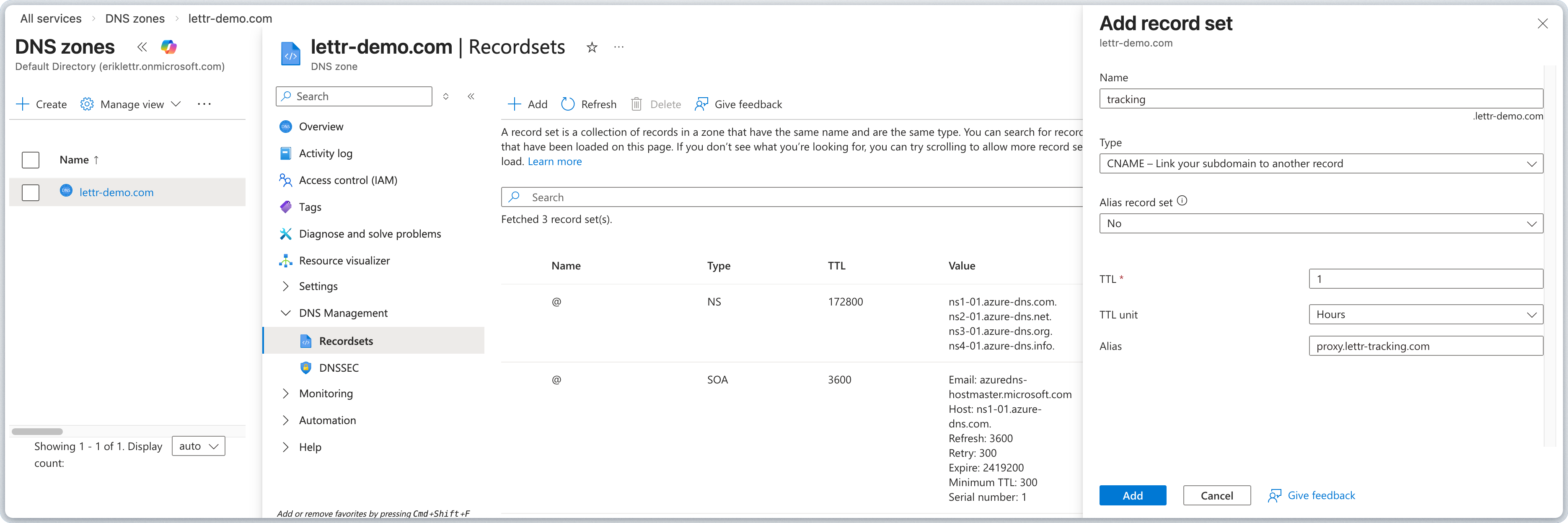
Azure DNS automatically appends your zone name to the record name. Always paste only the subdomain portion (e.g.
tracking, not tracking.company.com).Verify Your Tracking Domain
After adding both CNAME records, go back to Lettr and click Verify DNS Records. DNS propagation can take up to 24–48 hours, though it typically completes within a few minutes.Storage Domain Setup
A storage domain lets you serve email assets (images, attachments) from your own custom domain instead of the default Lettr storage URL. This requires two TXT records for certificate validation and ownership verification, and a CNAME record for routing asset requests to Lettr’s storage infrastructure.Add Storage Domain to Lettr
To create a Storage domain in Lettr:- Select Domains in the navigation panel
- Select Storage Domains
- Click Create Storage Domain
- Enter your desired storage subdomain (e.g.
assets.company.com) - Click Create Domain
Add TXT Record (Certificate Validation)
The Certificate Validation TXT record provisions an SSL certificate for your custom storage domain, enabling secure HTTPS delivery of email assets. Add the record in Azure DNS:- Click + Add in your DNS zone.
- Enter the Hostname from Lettr (without your domain suffix) into the Name field.
- Set Type to TXT.
- Leave TTL and TTL unit at their defaults (1 Hour).
- Enter the Value from Lettr into the Value field.
- Click Add.
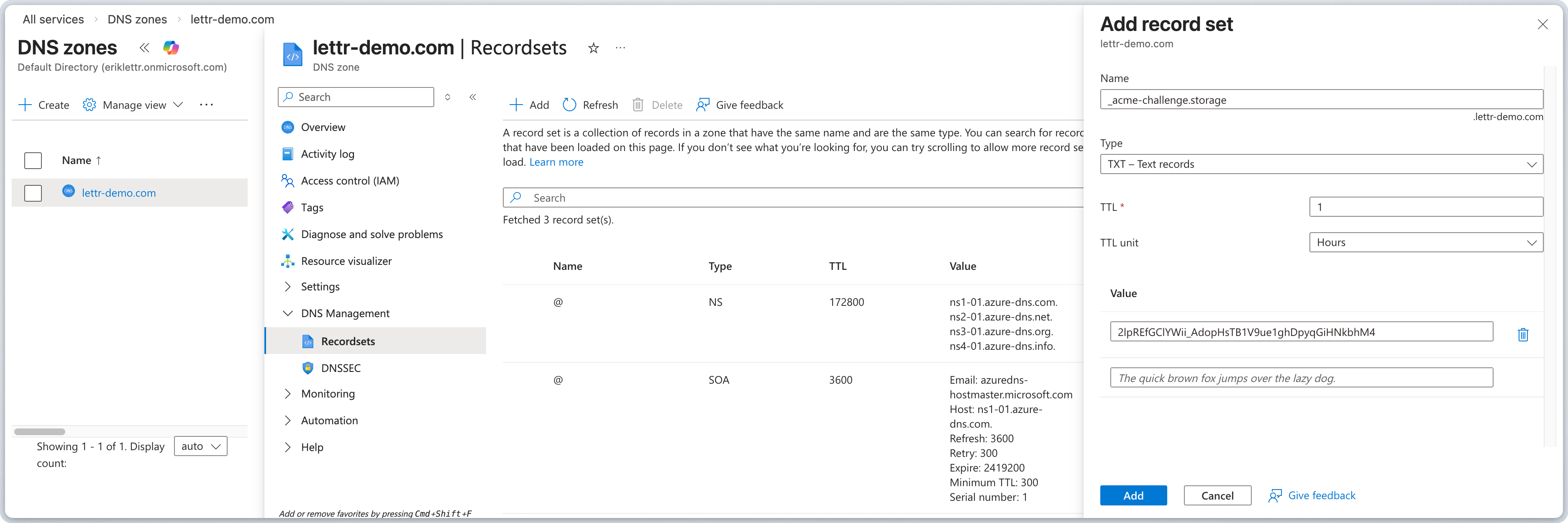
Azure DNS automatically appends your zone name to the record name. Always paste only the subdomain portion (e.g.
storage, not storage.company.com).Add TXT Record (Hostname Pre-validation)
The Hostname Pre-validation TXT record verifies ownership of the storage domain before Lettr provisions a custom hostname for it. Add the record in Azure DNS:- Click + Add in your DNS zone.
- Enter the Hostname from Lettr (without your domain suffix) into the Name field.
- Set Type to TXT.
- Leave TTL and TTL unit at their defaults (1 Hour).
- Enter the Value from Lettr into the Value field.
- Click Add.
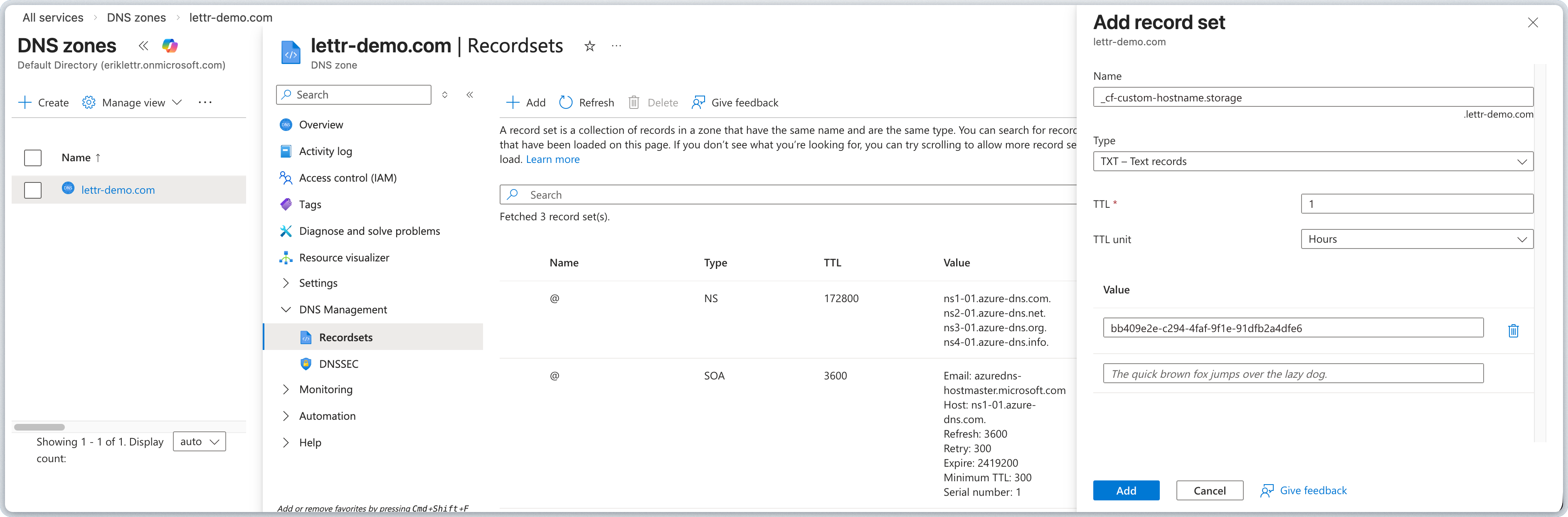
Azure DNS automatically appends your zone name to the record name. Always paste only the subdomain portion (e.g.
storage, not storage.company.com).Add CNAME Record (Domain Routing)
The Domain Routing CNAME record routes asset requests from your custom domain to Lettr’s storage infrastructure. Add the record in Azure DNS:- Click + Add in your DNS zone.
- Enter the Hostname from Lettr (without your domain suffix) into the Name field.
- Set Type to CNAME.
- Leave TTL and TTL unit at their defaults (1 Hour).
- Enter the Value from Lettr into the Alias field.
- Click Add.
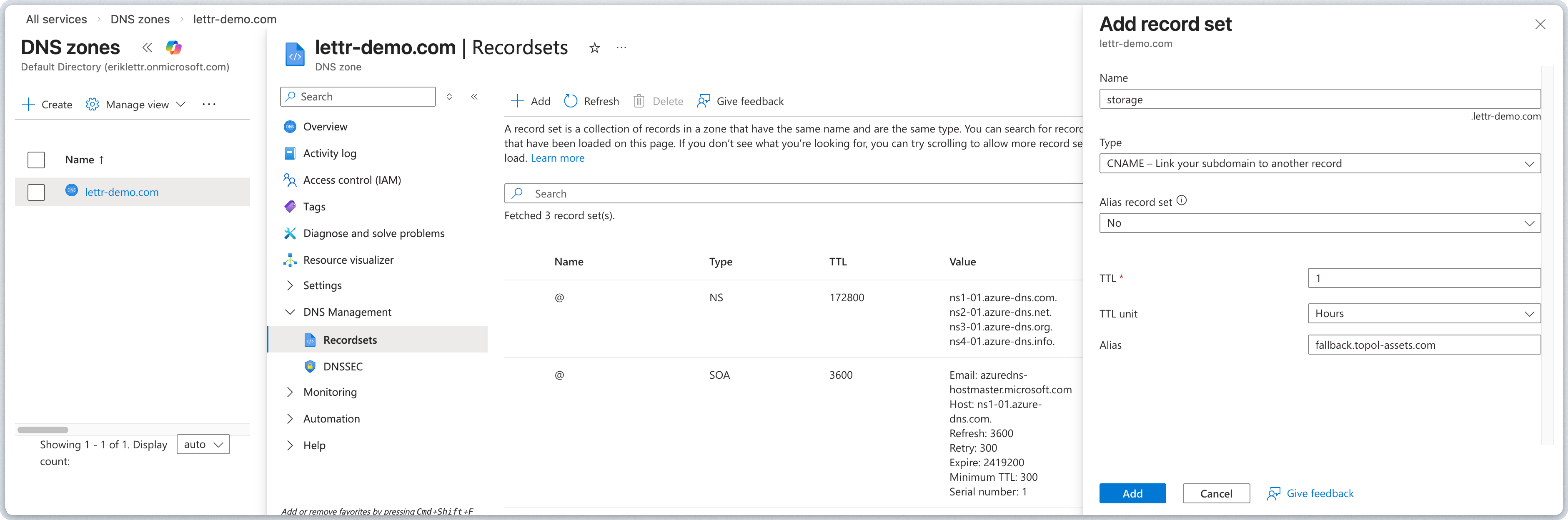
Azure DNS automatically appends your zone name to the record name. Always paste only the subdomain portion (e.g.
storage, not storage.company.com).Verify Your Storage Domain
After adding all three records, go back to Lettr and click Verify DNS Records. DNS propagation can take up to 24–48 hours, though it typically completes within a few minutes.Using Azure CLI
You can also add records using the Azure CLI. Replace<resource-group> and <zone-name> with your own values.
Troubleshooting
Permission Errors
Permission Errors
Ensure you have the DNS Zone Contributor role or equivalent permissions on the DNS zone resource in Azure.
Records Not Propagating
Records Not Propagating
Azure DNS typically propagates within minutes, but in some cases it can take longer. If verification fails after adding
records, check the following:
- Wait at least 30 minutes before your first verification attempt.
- Confirm the records exist using command-line tools:
- Use a web tool like dnschecker.org to verify propagation across multiple DNS servers worldwide.
Nameservers Not Pointing to Azure
Nameservers Not Pointing to Azure
If your records are saved in Azure DNS but not resolving, confirm that your domain registrar is pointing to Azure’s
nameservers. You can check this with:The output should include the four Azure nameservers shown in your DNS zone overview (e.g.
ns1-xx.azuredns.com). If it
shows a different provider’s nameservers, update them at your domain registrar.Wrong Record Type
Wrong Record Type
A common mistake is selecting the wrong type when creating the record set:
| Record | Correct Type |
|---|---|
| Sending verification | CNAME |
| DKIM | TXT |
| DMARC | TXT |
| Inbound mail | MX |
| Tracking SSL certificate | CNAME |
| Tracking traffic | CNAME |
| Storage certificate validation | TXT |
| Storage hostname pre-validation | TXT |
| Storage domain routing | CNAME |
DKIM Value Truncated
DKIM Value Truncated
The DKIM TXT value is a long string. After saving the record set in Azure, re-open it to confirm the full value was
stored. If it appears truncated, delete the record and re-add it, pasting the full value carefully.
When to Contact Support
When to Contact Support
If your DNS records are correctly configured (confirmed with
dig or dnschecker.org) and verification still fails after
48 hours, contact Lettr support at support@lettr.com or through the in-app chat. Include your domain name and the
output of the dig commands above.Related Topics
Sending Domains
Learn about sending domain setup, SPF, DKIM, and DMARC.
Inbound Domains
Configure MX records to receive emails with Lettr.
Tracking Domains
Set up a custom tracking domain for click and open tracking.
Storage Domains
Serve email assets from your own custom domain.
Domains Overview
Understand domain types and how they work in Lettr.
Domain Verification Failures
Troubleshoot common DNS configuration and propagation issues.